The Top 5 LTE Protection Domains
Security has become a hot topic among LTE operators. While the attention focuses almost exclusively on mobile devices, they are far from being the only targets for attack and entry points to mobile networks. Attacks can be launched from the RAN and the Internet, as well as from roaming and MVNO partners. The infographic available on Slideshare here, created by Stoke illustrates these threat domains and the needed protection.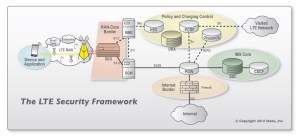
To avoid congestion or service interruption, and provide a consistent QoE to their subscribers, mobile operators have to protect their entire networks – devices, base stations or femto cells, backhaul links, and the core network – against abnormal traffic flows that may stem from intentional attacks (e.g., malware), unintended events (e.g., configuration errors), or unusual but legitimate traffic spikes (e.g., during a sports event), and may result in spikes both in the control plane (signaling floods) and in the data plane (RAN congestion). In the context of end-to-end network protection, securing the radio-to-core link is of crucial importance to ensuring the overall security in mobile networks.
LTE operators have invested heavily in protecting the subscriber and the network in five key areas.
Device and Application:
User equipment must be authenticated by the core network before enabled to make voice calls, texting, Internet browsing or access any other service through the mobile network. This helps prevents fraudulent use of subscriber services by an unauthorized user or different device.
RAN-Core Border:
A security gateway (SEG) provides secure aggregation of traffic and ensures correct authentication of cell sites. The 60M small cells expected to be deployed by 2016 will be especially vulnerable.
IMS Core and Policy and Charging Control:
Policy Charging and Control Elements provide secure access to authorized services and accurate billing. IP Multimedia Subsystems enable voice over LTE (VoLTE) and ensure that only authorized sessions are allowed access.
Internet Border:
Firewalls, IDS and security gateways are deployed to protect against DDoS attacks that can cause widescale service outages or otherwise disrupt service access and quality.
Security and, more generally, network protection from unexpected high-traffic events has gained a higher priority status in LTE as mobile networks become easier and more attractive targets for malicious attacks, and more vulnerable to signaling and data traffic overload that can disrupt or completely block network access.
Within the context of LTE security, the radio-to-core link has to be protected to ensure end-to-end network security. The security gateway is a crucial enabler to provide the scalability, processing and aggregation capabilities, the performance, and the functionality to support IPsec.
An increasing number of operators are choosing to deploy IPsec across both trusted and untrusted sites as they recognize that even trusted sites can become targets of security threats.
